-
-
Notifications
You must be signed in to change notification settings - Fork 239
Feature overview
It's quite difficult to summarize all the features of EMBA, simply because there are too many of them. Therefore, all modules (which are the core of EMBA) will be listed in the correct order of (non-parallel) execution and briefly described.
These modules will be loaded and called before anything else. Their primary task is to extract firmware out of files/archives and to search for basic information, such as how many files and binaries are available.
-
P02 Basic binary firmware analyzer
Gives some very basic information about the provided firmware binary. The main tasks currently are: -
P05 archive extractor
If EMBA identify a *.zip, *.tar or *.tgz archive, then it will be extracted with patool. -
P10 VMDK extractor
If EMBA was able to identify a VMDK image it tries to mount it viaguestmount. If this mount was successful, the content will get copied to the firmware directory in the EMBA log directory for further analysis. -
P14 Mount ext2 images
Mounts and copies ext images to your disk. Using binwalk with those images kills the permissions and the symlinks and therefore mounting and copying them is the better choice. -
P15 UBI filesystems extractor
Extracts UBI filesystems via ubireader_extract_images and ubireader_extract_files. -
P17 Extract gpg compressed images
Extracts gpg compressed firmware images (mostly seen to be used by Linksys/Belkin). -
P19 Mount BSD UFS images
Mounts and copies BSD UFS images to your disk. -
P20 Foscam Decryptor
Extracts encrypted firmware images from the vendor Foscam. -
P21 Buffalo Decryptor
Extracts encrypted firmware images from the vendor Buffalo. -
P22 Extracts Zyxel firmware updates images
See also the DEF CON 30 Talk - Tear Down this Zywall: Breaking Open Zyxel Encrypted Firmware by Jay Lagorio for further details. -
P23 Mount Qemu QCOW2
Mounts and extracts Qemu QCOW2 images. -
P25 Extracts Android OTA update files
Generates filesystem directory with payload_dumper -
P35 UEFI Extractor
Extracts UEFI images with BIOSUtilities. -
P55 Unblob firmware extractor This module uses the unblob firmware extractor for extracting the firmware file.

-
P60 Binary firmware extractor
If the extraction process of EMBA was failing this module walks through all files and tries to extract every file with the corresponding extractor module - this is the so called deep extraction mode. -
P65 Package extractor Searches for typical package archives like *.deb, *.ipk or *.apk and extracts them to the root directory.

-
P99 Binary firmware basic analyzer
This module performs some last preparation tasks before starting the analysis through the Core modules.
These are the core modules of EMBA. This includes checks for possible vulnerabilities, hardening measures or just interesting details of the firmware. These modules are currently optimized for Linux systems.
-
S02 UEFI FwHunt
Uses FwHunt for identification of vulnerabilities in possible UEFI firmware images. -
S05 Firmware and testing details
Counts the number of files and executables in firmware and stores the firmware structure in the log files. It also searches through possible release filesconfig/release_files.cfgfor operating system identifiers. -
S06 Linux distribution detection
Checks for typical marker of known distributions like Kali Linux, Debian or OpenWRT. -
S09 Binary firmware version detection
Iterates through all binaries of the firmware and does static version detection. These versions are used from the F20 module to detect outdated software components and the corresponding vulnerabilities (CVE) and possible exploits.

-
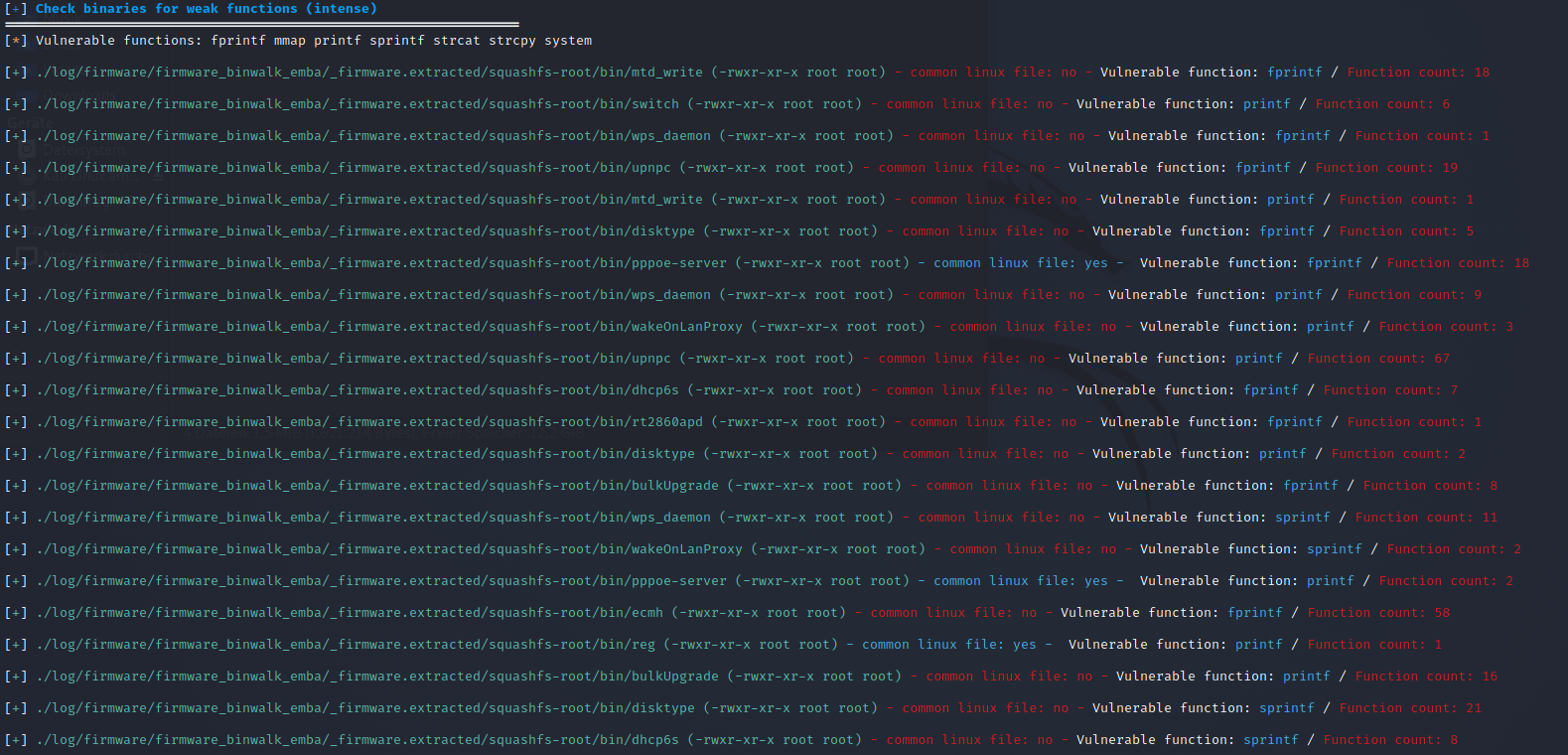
S10 Check binaries
This module was the first module that existed in EMBA. The main idea is to identify the binaries that are using interesting and weak functions (e.g. strcpy) and to establish a ranking of areas to look at first.

-
S12 Binary protection check
This module checks for protection mechanisms in the identified binaries via checksec.

-
S13 Weak function check
This module was the extended S10 module. It iterates through all executables and generates a disassembly with objdump. This disassembly is further analysed for interesting functions likestrcpy(defined inhelpers.cfg). Additionally it counts these functions and shows which binary uses which function most.

If this module failes using objdump, the module S14 tries to disassemble the binaries with radare2. -
S14 Weak function check with radare2
As S13 it iterates through all executables and generates a disassembly with radare2. All other steps are quite similar to S13. As the module runs quite long with high CPU load it only gets executed when the objdump module fails. -
S15 Check bootloader and system startup
Scans for device tree blobs, bootloader and startup files and checks for the default runlevel. -
S20 Check shell scripts with shellchecker
Checks for bugs, stylistic errors, etc. in shell scripts, then it lists the found error types.

-
S21 Check python scripts with pylint
Checks for bugs, stylistic errors, etc. in python scripts, then it lists the found error types. -
S22 Check php scripts with progpilot
Checks for bugs, stylistic errors, etc. in php scripts, then it lists the found error types. It also checks thephp.inifile. -
S24 Find kernel and startup parameters in extracted files
Identifies the kernel file and the init command line. -
S25 Check kernel
Determines kernel version and description and checks for kernel configuration. It uses linux-exploit-suggester to check for possible kernel exploits and analyzes kernel modules to find which license they have and if they are stripped. It also looks for themodprobe.ddirectory and lists its content.

-
S35 Check HTTP files
Searches for http and webserver (Apache, nginx, Lighttpd, etc.) related files and checks forphp.ini. -
S40 Search files with weak permissions
Scans the firmware for setuid, setgid, world writable and shadow files and checks if allrc.dandinit.dfiles have weak permissions. -
S45 Search password files
Searches for password related files and tries to extract passwords and root accounts. -
S50 Check users, groups and authentication
Checks for users with UID 0; for non-unique accounts, group IDs, group names; scans all available user accounts and possible NIS(+) authentication support. It looks upsudoersfile and analyzes it for possible vulnerabilities. It also searches for PAM authentication files and analyze their usage. -
S55 Search history files
Searches for possible history files like.bash_history. -
S60 Search certification files and other interesting stuff
Scrapes firmware for certification files and their end date. On outdated certificates it prints a warning. -
S65 Search/scan config file
Scans system for typical config files, e.g.*.cfgorfstaband analyzesfstabfor user details. -
S70 Search hidden files
Searches for all hidden files in the firmware. -
S75 Search network configs
A more exceptional search for files likeresolv.conf,iptables.confandsnmpf.confand analyzes their content. Checks systemd network configuration files. -
S80 Check cronjobs
Examine all files for cronjob configuration, e.g.cronorcrontaband lists their jobs and other possible intriguing details. -
S85 Check SSH
Searches for ssh-related files and squid configuration files. Additionally it tests found sshd configuration files with sshdc. -
S90 Search Mail files
Searches in/var/mailfor mail files. -
S95 Check interesting binaries
Searches explicitly for binaries likegccorgdband also binaries for post exploitation likewgetorftp. -
S100 Search areas for command injection
Looks for web-based files in folders likewwwand searches for very basic code execution patterns inside of them. This module is currently in a very early state and needs massive improvements. -
S106 Deep analysis of files for private keys
Searches for files with a private key inside. -
S107 Deep analysis of files for password hashes
Tests all firmware files for password hashes. -
S108 Deep analysis of files for password hashes with stacs
Tests all firmware files for password hashes with thestacsengine and the corresponding community ruleset. -
S110 Check for code patterns with yara
Checks files with yara for suspicious patterns. -
S115 Software component and version detection via usermode emulation
Emulates firmware executables with qemu to identify version details. This module and needs to be activated separately via the-Eswitch. It is also recommended to only use this technique in a dockerized environment. -
S116 Extract version information from S115
Analyzes the results from the user-mode emulator (S115) and extracts version details. Learn more about the emulator.
Learn more about the emulator. -
S120 Check binaries with cwe-checker
Runs cwe-checker to check binary for common bug classes such as vicious functions or integer overflows. As the runtime is quite long, it needs to be activated separately via-cswitch.
These modules are trying to emulate the embedded device in system emulation mode. See also this wiki page for further details.
These modules are the last ones in an EMBA run. They are used for summarizing and presenting an overview of the results of previous modules.
-
F10 License summary
Collects license details and gives a list with binaries, identified version and the corresponding license (if available). The license details are maintained in the configuration fileconfig/bin_version_strings.cfg.

-
F20 Final CVE aggregator
Aggregates all found version numbers together from S06, S09, S25 and S116 and searches with cve-search for known vulnerabilities. Finally it checks multiple sources for known exploits that could possible be used against the target system.
 Learn more about the aggregator.
Learn more about the aggregator. -
F21 CycloneDX SBOM converter This module generates a minimal json SBOM from the identified software inventory via cyclonedx.

-
F50 Final aggregator
Generates the final summary and report of the firmware analysis.

 Learn more about the aggregator.
Learn more about the aggregator.
EMBA - firmware security scanning at its best
Sponsor EMBA and EMBArk:
The EMBA environment is free and open source!
We put a lot of time and energy into these tools and related research to make this happen. It's now possible for you to contribute as a sponsor!
If you like EMBA you have the chance to support future development by becoming a Sponsor
Thank You ❤️ Get a Sponsor
You can also buy us some beer here ❤️ Buy me a coffee
To show your love for EMBA with nice shirts or other merch you can check our Spreadshop
EMBA - firmware security scanning at its best
