Summary
when jadx parses a resource file, there is an escape problem with the style file, which can overwrite other files in the directory when saving the decompile result.
Although I don't think this vulnerability realizes path traversal in the true sense of the word , I reported it anyway
Details
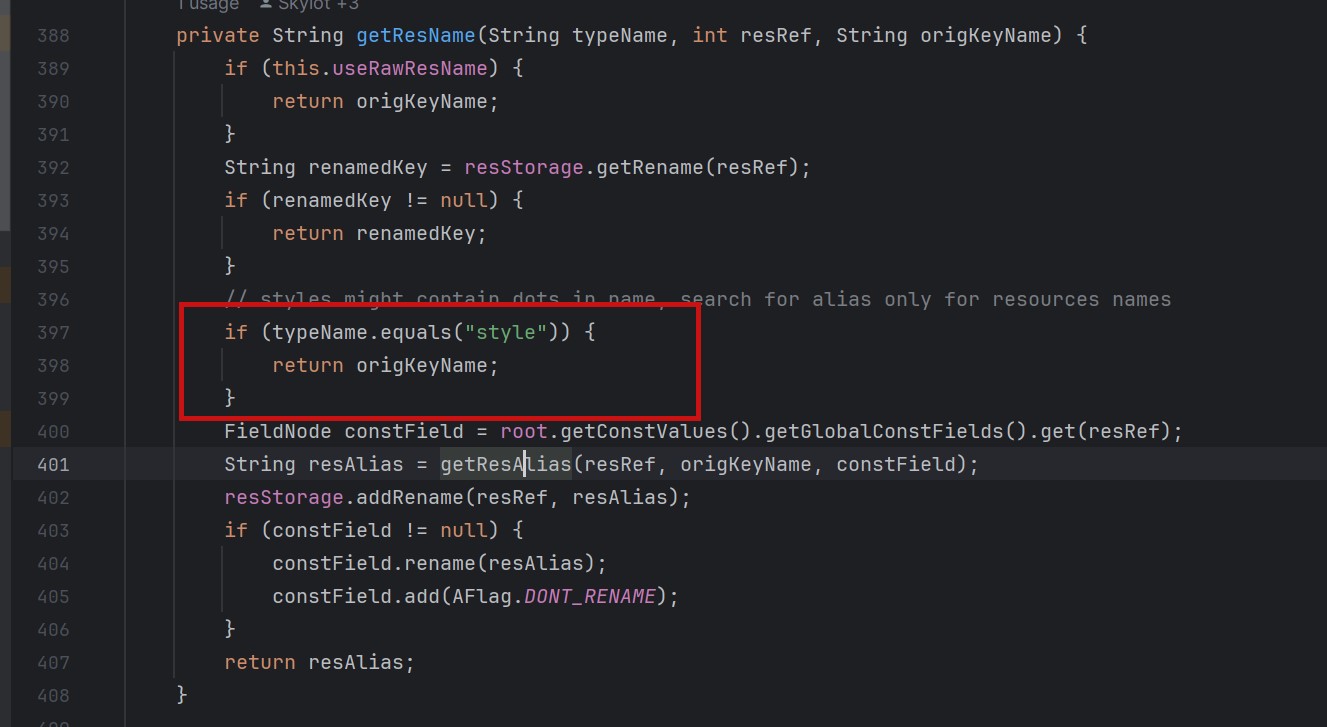
I see that getResAlias does something with the filename.
private String getResAlias(int resRef, String origKeyName, @Nullable FieldNode constField) {but type style will return the original filename directly.
so our goal is to take a malicious file that was originally of type raw, modify its type to style, trick jadx into
step1
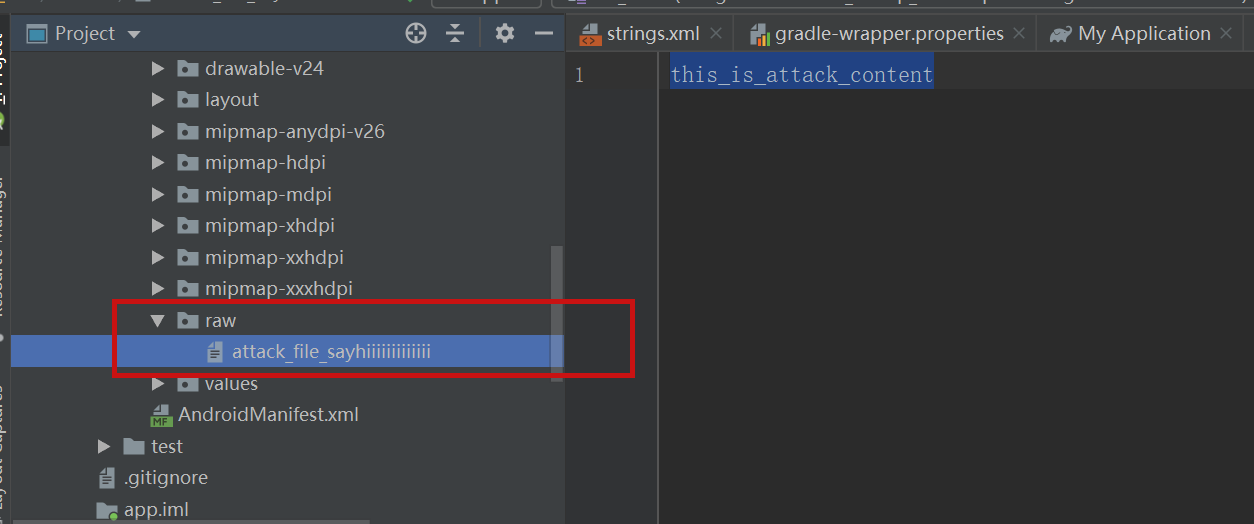
create an android project using androidstudio and create a raw folder with the name attack_file_sayhiiiiiiiiiiiii, it doesn't matter what the content is!
generate an initial APK
step2
extract this initial APK using ZIP software to get resources.arsc

drop resources.arsc into 010editor
step3
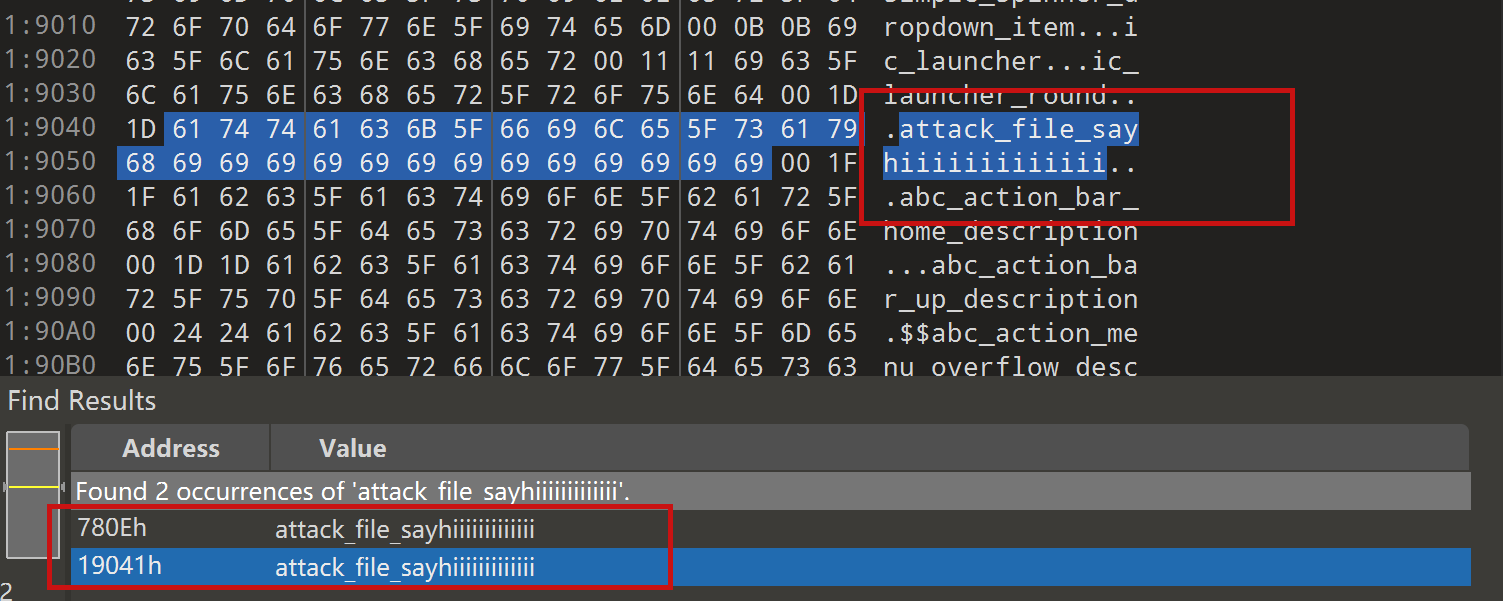
search for the previous filename attack_file_sayhiiiiiiiiiiiii , two will appear here, we choose the second one
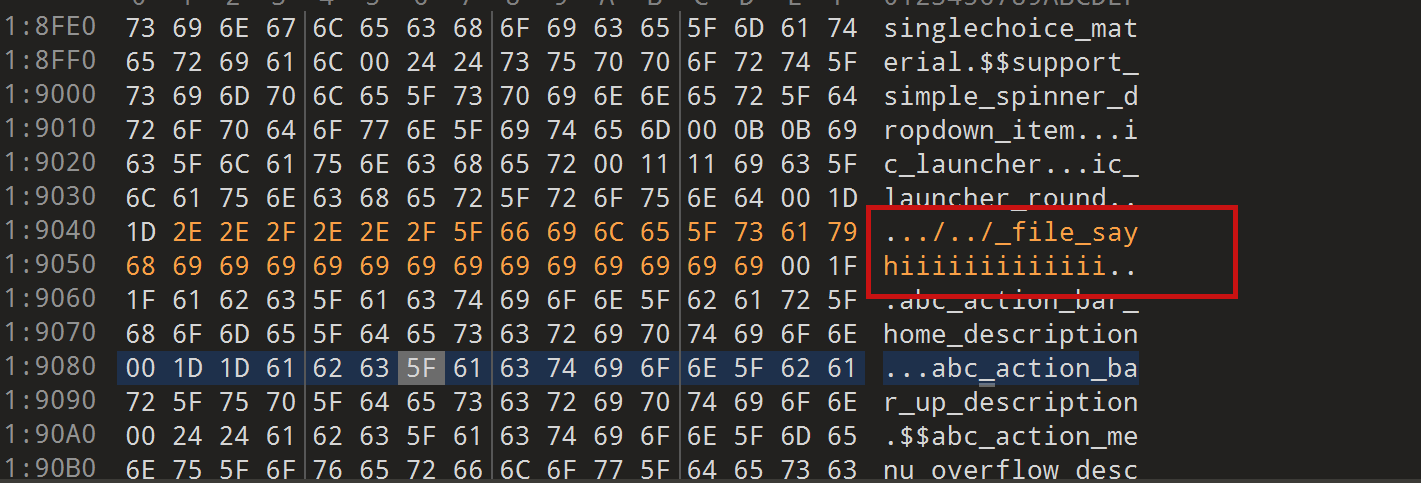
let's change the name of the file here. I'll change it to ../../_file_sayhiiiiiiiiiiiii
note that you can only overwrite files in the folder where the decompile was saved.
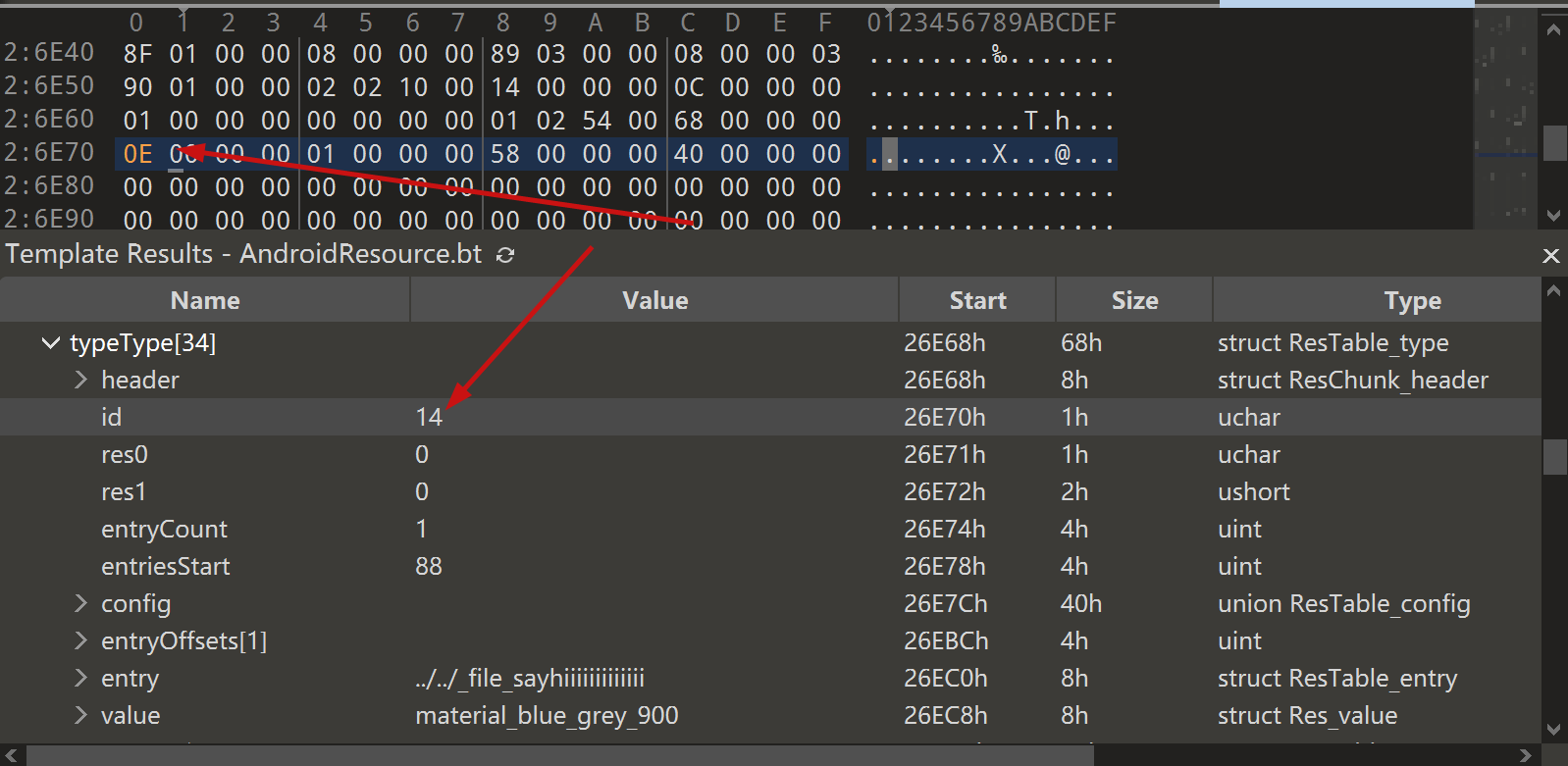
step4
change the type of this file to style
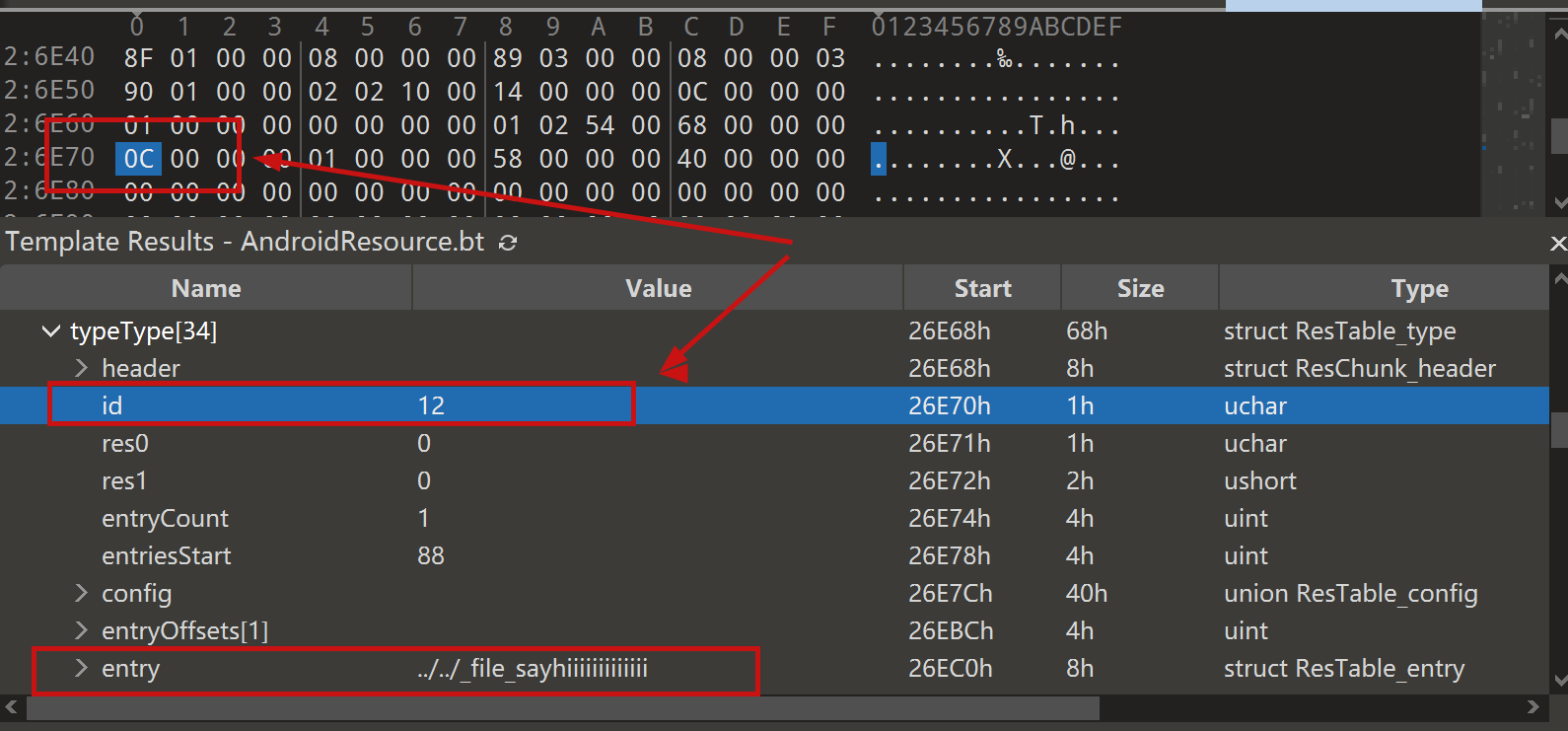
modified to 0E
step5
After saving, re-compress the whole folder into a zip, then change the extension to APK.
open it with JADX and you can see that it has been changed to a style type.
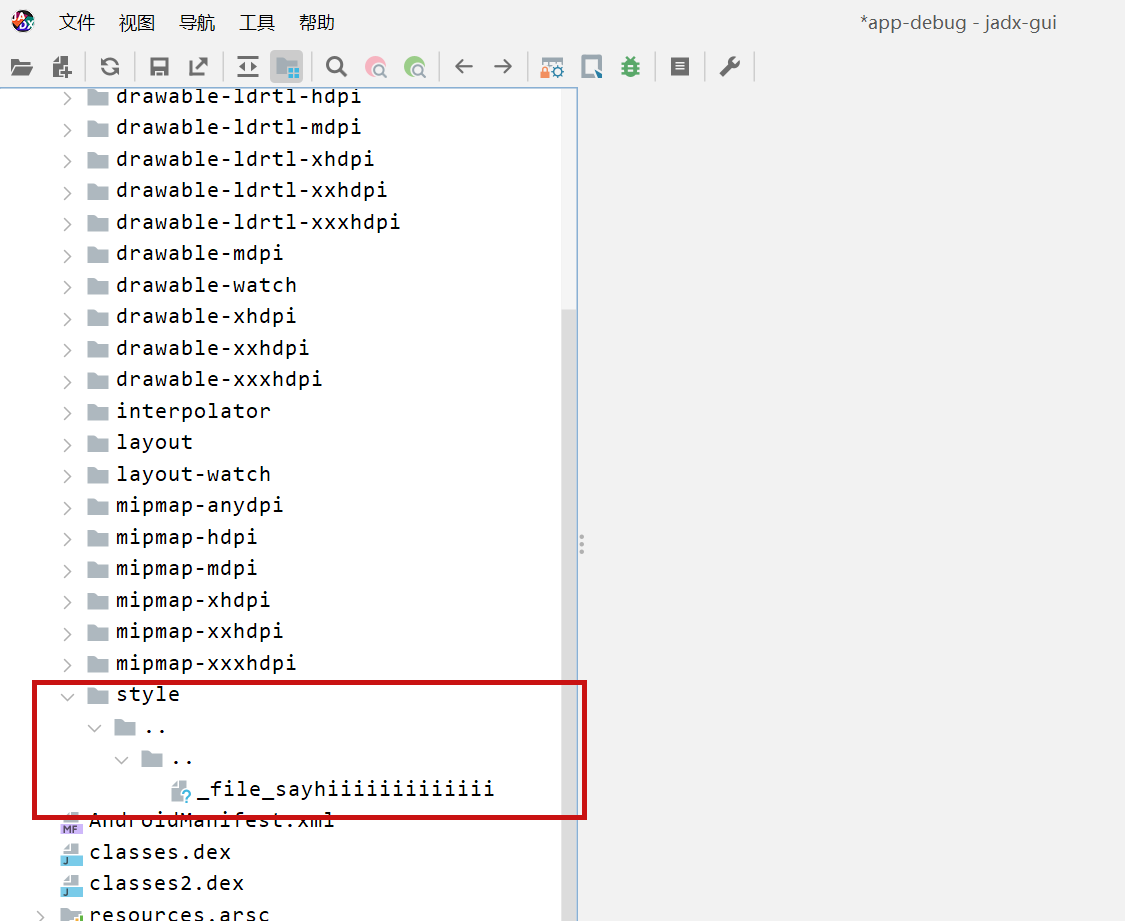
click save all
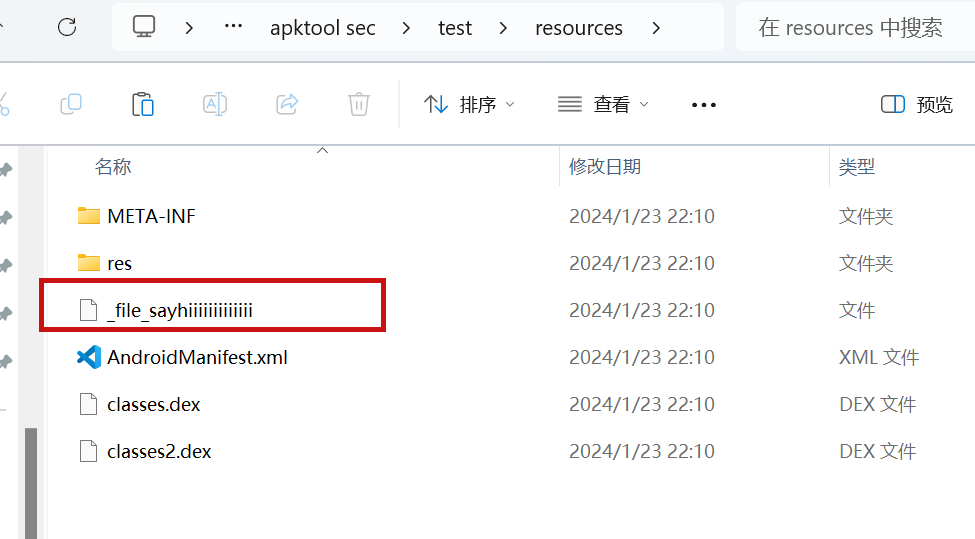
you can see the file escaping.
so we can also construct a
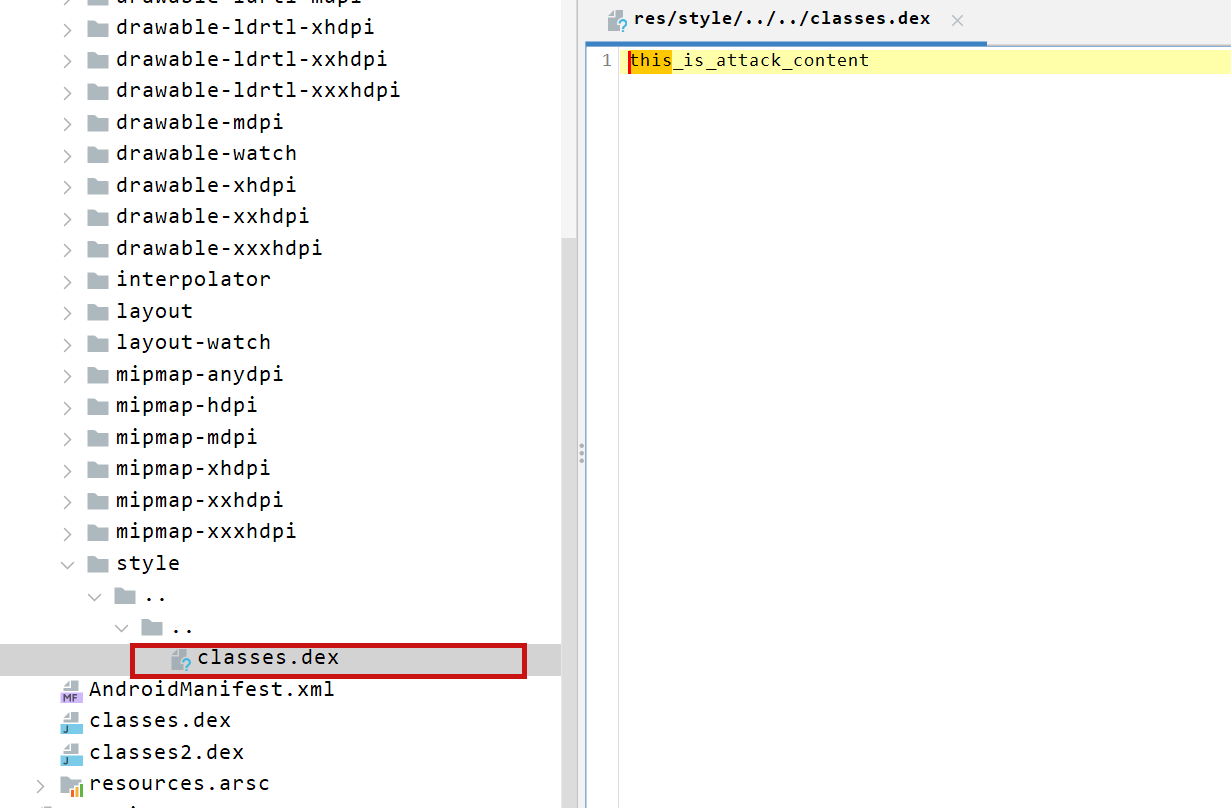
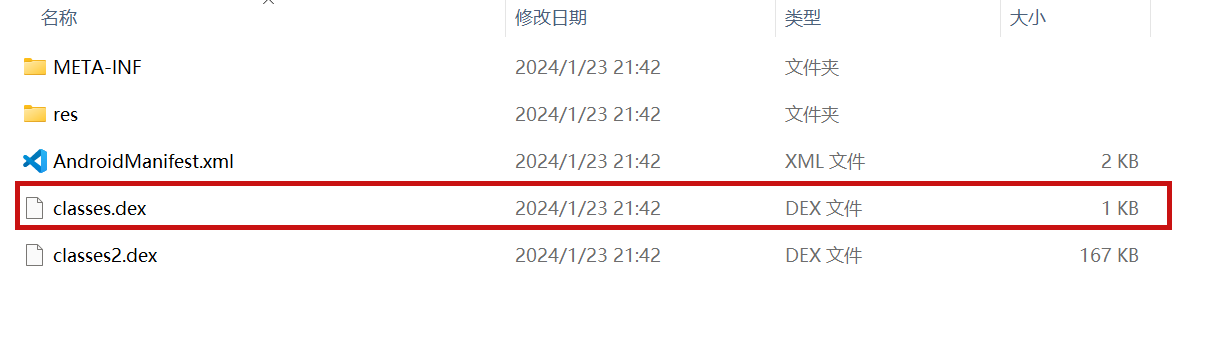
so the classes.dex file is also replaced here
PoC
the details above have been written
Impact
latest version
References
Summary
when jadx parses a resource file, there is an escape problem with the style file, which can overwrite other files in the directory when saving the decompile result.
Although I don't think this vulnerability realizes path traversal in the true sense of the word , I reported it anyway
Details
I see that getResAlias does something with the filename.
but type style will return the original filename directly.
so our goal is to take a malicious file that was originally of type raw, modify its type to style, trick jadx into
step1
create an android project using androidstudio and create a raw folder with the name attack_file_sayhiiiiiiiiiiiii, it doesn't matter what the content is!
generate an initial APK
step2
extract this initial APK using ZIP software to get resources.arsc
drop resources.arsc into 010editor
step3
search for the previous filename attack_file_sayhiiiiiiiiiiiii , two will appear here, we choose the second one
let's change the name of the file here. I'll change it to ../../_file_sayhiiiiiiiiiiiii
note that you can only overwrite files in the folder where the decompile was saved.
step4
change the type of this file to style
modified to 0E
step5
After saving, re-compress the whole folder into a zip, then change the extension to APK.
open it with JADX and you can see that it has been changed to a style type.
click save all
you can see the file escaping.
so we can also construct a
so the classes.dex file is also replaced here
PoC
the details above have been written
Impact
latest version
References